Spear phishing takes the practice of cyber deception to new levels by using real people as the fake lure.
Doctor Digital Says

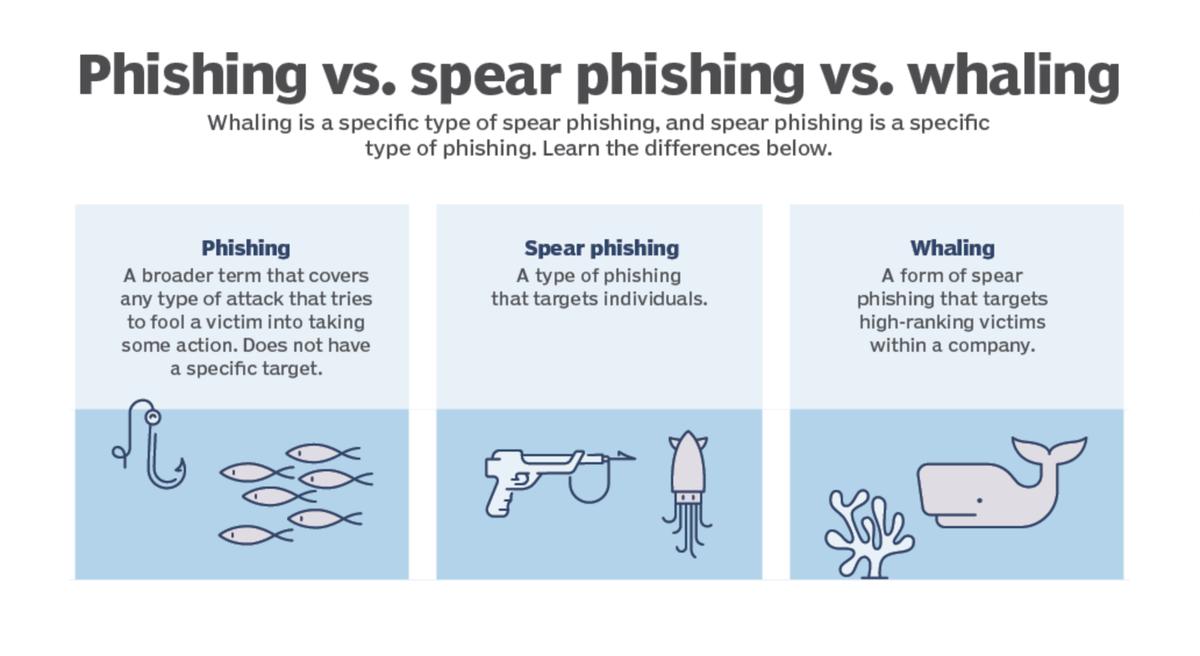
In the ever-evolving landscape of cyber threats, spear phishing has emerged as one of the most deceptive and cunning methods employed by cybercriminals. Unlike traditional phishing attacks that cast wide nets in hopes of catching a few victims, spear phishing targets specific individuals or organisations with personalised and convincing messages. This dangerous technique has wreaked havoc on businesses of all sizes, especially small and medium-sized enterprises (SMEs) that may lack the robust cybersecurity infrastructure of larger corporations. In this blog post, we will delve into the insidious nature of spear phishing, its detrimental impact on SMEs, and offer practical strategies to safeguard against this malicious threat.
Understanding Spear Phishing
Spear phishing is a targeted form of cyber attack that exploits social engineering techniques to gain unauthorised access to sensitive information, such as login credentials, financial data, or confidential business information. The perpetrators use personalised and seemingly legitimate emails, messages, or even social media interactions to deceive the recipient into believing the communication is from a trusted source. These messages often contain relevant information to the recipient, such as the recipient's name, position, or references to recent events, making it challenging to distinguish them from legitimate communications.
How Spear Phishing Works
- Research: Cybercriminals begin by conducting extensive research on their targets. They scour the internet and social media platforms to gather personal and professional information, including email addresses, connections, and interests.
- Crafting the bait: Armed with the acquired knowledge, the attackers craft highly personalised emails or messages that appear genuine and relevant to the recipient. These messages may contain links to malicious websites, infected attachments, or requests for sensitive information.
- Luring the victim: The attackers deploy social engineering tactics to manipulate the target's emotions, curiosity, or sense of urgency. They might impersonate trusted colleagues, vendors, or even senior executives to trick the recipient into taking the desired action.
- Exploiting the vulnerability: Once the target takes the bait and interacts with the malicious content, the attackers exploit vulnerabilities in the target's systems to steal information, install malware, or gain unauthorised access to sensitive data.
Impact on Small and Medium-Sized Businesses
SMEs are particularly susceptible to spear phishing attacks due to their limited resources and often underdeveloped cybersecurity infrastructure. The consequences of falling victim to such attacks can be dire:
- Financial Losses: Spear phishing attacks can lead to financial losses resulting from fraud, unauthorised fund transfers, or ransom payments to regain access to critical data.
- Reputational Damage: A successful spear phishing attack can tarnish an SME's reputation, eroding customer trust and loyalty.
- Data Breaches: Sensitive business and customer data can be exposed, leading to legal liabilities and potential regulatory fines.
- Business Disruption: Infiltration by spear phishers may disrupt normal business operations, causing downtime and loss of productivity.
- Opportunity Costs: Dealing with the aftermath of a spear phishing attack diverts resources and focus away from core business activities.
Protecting Against Spear Phishing Attacks
While spear phishing attacks are highly sophisticated, there are proactive measures that individuals and businesses can take to protect themselves:
- Employee Training: Conduct regular cybersecurity training sessions for all employees, emphasising the importance of verifying the authenticity of emails and messages before clicking on links or sharing sensitive information.
- Multi-Factor Authentication (MFA): Implement MFA for accessing critical systems and data. This extra layer of security makes it significantly more challenging for attackers to gain unauthorised access, even if they obtain login credentials.
- Email Filtering and Security Solutions: Invest in robust email filtering and security solutions that can detect and block suspicious emails before they reach employees' inboxes.
- Encourage a Culture of Suspicion: Encourage employees to maintain a healthy skepticism towards unsolicited emails and messages, especially those that request sensitive information or create a sense of urgency.
- Keep Software Up to Date: Regularly update operating systems, applications, and security software to protect against known vulnerabilities that attackers might exploit.
- Encryption: Use encryption for sensitive data, both in transit and at rest, to ensure that even if intercepted, the information remains unreadable to unauthorised parties.
Spear phishing continues to be a significant threat to businesses worldwide, with SMEs being particularly vulnerable to its cunning tactics. As cybercriminals evolve their methods, it is crucial for organisations to stay ahead by fostering a cybersecurity-aware culture and implementing robust protective measures. By empowering employees with the knowledge and tools to recognise and resist spear phishing attempts, SMEs can effectively defend against this stealthy cyber threat and safeguard their assets, reputation, and future prosperity.